The rise of mobile technology has fundamentally changed how we connect, communicate, and access information. However, this increased reliance on wireless connectivity – particularly guest wireless networks – presents both opportunities and challenges. A robust and clearly defined Guest Wireless Acceptable Use Policy Template is crucial for protecting your organization's assets, ensuring fair access for all users, and mitigating potential risks. This template provides a framework for establishing guidelines and expectations regarding the use of wireless networks, safeguarding your business and its customers. It's more than just a policy; it's a proactive measure demonstrating your commitment to responsible technology usage. This document aims to offer a comprehensive and adaptable solution for managing guest wireless networks, ensuring a secure and compliant environment. Understanding the nuances of your specific business and its users is key to crafting an effective policy. Let's delve into the essential components of a successful Guest Wireless Acceptable Use Policy Template.
Understanding the Landscape of Guest Wireless
Before establishing a policy, it's vital to understand the diverse range of guest wireless networks operating within your organization. These networks often lack the same level of security and monitoring as corporate-owned networks. The risk of unauthorized access, data breaches, and misuse is significantly higher. Furthermore, guest networks frequently utilize less secure protocols and configurations, making them vulnerable to various threats. A well-defined policy addresses these concerns head-on, establishing clear expectations and providing mechanisms for detection and response. Consider the types of devices commonly used – smartphones, tablets, laptops – and the typical usage patterns. Are guests primarily for business purposes, or are they primarily for leisure activities? This initial assessment will inform the specific guidelines you implement. Many organizations also utilize different levels of security, ranging from basic Wi-Fi encryption to more advanced VPN solutions.
Key Components of a Comprehensive Policy
A truly effective Guest Wireless Acceptable Use Policy Template should encompass several key elements. These aren't just a checklist; they represent a strategic approach to managing guest network access.
- Acceptable Use: This section clearly defines what is and isn't permitted during guest network usage. It should explicitly prohibit activities such as downloading unauthorized software, accessing inappropriate content, engaging in illegal activities, or using the network for personal gain.
- Device Restrictions: Specify the types of devices allowed on the network. Typically, guest networks are restricted to smartphones, tablets, and laptops. Restrictions may apply to devices with outdated operating systems or known vulnerabilities.
- Wi-Fi Security: Emphasize the importance of strong passwords and encryption. Recommend using WPA2 or WPA3 encryption for all guest networks. Consider implementing a guest network firewall to further enhance security.
- Data Protection: Outline procedures for protecting sensitive company data. This includes requiring guests to use a separate, secure account for accessing company resources. Discourage the sharing of passwords or other confidential information.
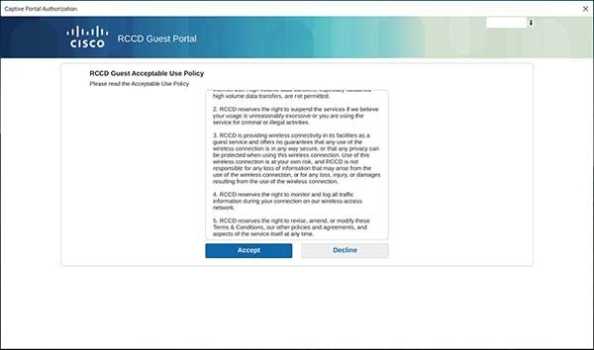
- Monitoring and Enforcement: Detail how the policy will be monitored and enforced. This may involve using network monitoring tools to detect suspicious activity, implementing a reporting mechanism for guests to report violations, and establishing consequences for policy violations.
- Guest Identification: Establish a process for identifying guests. This could involve requiring guests to register with a system or using a unique device ID. This helps track usage and potentially identify unauthorized access.
Detailed Policy Guidelines – Protecting Your Assets
Let's examine some specific guidelines that should be integrated into your Guest Wireless Acceptable Use Policy Template.
Access Control and Authentication
The cornerstone of any secure network is proper access control. Guests should be granted access to the network only when necessary. A strong authentication method is essential. This typically involves requiring guests to enter a unique password, which should be changed upon initial setup. Consider implementing multi-factor authentication (MFA) for enhanced security. Regularly review and update access permissions to ensure that only authorized users have access to specific resources.
Data Usage Restrictions
Guest networks are inherently less secure than corporate networks, so strict data usage restrictions are paramount. Guests should be prohibited from downloading or uploading files to the network. This includes applications, software, and any other data that could compromise company information. Furthermore, guests should be instructed to avoid accessing sensitive company data, such as financial records, customer information, or intellectual property. A clear policy on data retention is also crucial.
Network Usage Guidelines
The policy should outline acceptable network usage patterns. For example, guests should refrain from streaming video, playing online games, or engaging in other activities that consume excessive bandwidth. Consider implementing bandwidth throttling to limit the amount of data that can be transferred. Regularly monitor network usage to identify potential issues and ensure compliance with the policy.
Reporting and Incident Response
Establish a clear process for guests to report any suspected security breaches or policy violations. Provide a dedicated contact point for reporting issues. Respond promptly and effectively to all reports, investigating the situation thoroughly and taking appropriate action. Document all incidents and resolutions. This demonstrates a commitment to security and provides valuable insights for improving the policy.
Device Restrictions – Beyond Basic Security
While basic device restrictions are important, consider adding more specific guidelines. For example, guests should not use personal devices (smartphones, tablets, laptops) to access company resources. This helps prevent the potential for malware infections and data breaches. It's also advisable to restrict the use of USB drives, as they can be easily exploited for data theft.
The Importance of Training and Communication
Simply having a policy isn't enough. Effective communication and training are essential for ensuring that guests understand and comply with the policy. Provide training sessions to educate guests about the risks associated with guest wireless networks and the importance of adhering to the policy. Regularly remind guests of the policy and address any questions or concerns they may have. A well-communicated policy fosters a culture of security awareness and promotes responsible network usage.
Monitoring and Enforcement – Continuous Improvement
The effectiveness of a Guest Wireless Acceptable Use Policy Template depends on ongoing monitoring and enforcement. Regularly review the policy and its implementation to ensure that it remains relevant and effective. Use network monitoring tools to detect suspicious activity and identify potential policy violations. Implement a system for tracking policy compliance. Consider using automated tools to enforce policy restrictions. Don't hesitate to issue warnings or disciplinary action for policy violations. A proactive approach to enforcement is crucial for maintaining a secure and compliant network.
Conclusion
Effective management of guest wireless networks requires a proactive and well-defined policy. A comprehensive Guest Wireless Acceptable Use Policy Template provides a solid foundation for establishing clear expectations, mitigating risks, and protecting your organization's assets. By incorporating the key components outlined in this article, you can create a policy that effectively balances guest access with security and compliance. Remember that a policy is not a static document; it should be regularly reviewed and updated to reflect changing business needs and security threats. Continuous monitoring, training, and enforcement are essential for maintaining a secure and compliant guest wireless network. Investing in a robust policy is an investment in the long-term security and success of your organization. Ultimately, a thoughtful and well-executed policy demonstrates a commitment to responsible technology usage and fosters a culture of security awareness among your guests.
0 Response to "Guest Wireless Acceptable Use Policy Template"
Posting Komentar