
The concept of a "Free Certificate of Destruction" might conjure images of dystopian futures or criminal activity. However, in the realm of legitimate, albeit specialized, applications, this template offers a surprisingly versatile tool for precisely controlled and documented destruction. It's crucial to understand that this template is designed for situations requiring meticulous record-keeping and adherence to legal requirements. It's not a tool for casual destruction; it's a means of ensuring accountability and minimizing potential harm. This article will delve into the various aspects of this template, exploring its functionality, potential uses, and important considerations. Free Certificate Of Destruction Template – a powerful, albeit carefully regulated, option for specific scenarios.
The rise of digital data destruction has spurred a growing demand for reliable and verifiable methods of eliminating sensitive information. Traditional methods like shredding can be cumbersome and often lack the necessary documentation. A dedicated "Free Certificate of Destruction Template" provides a structured and easily trackable way to ensure that data is permanently removed, minimizing the risk of unauthorized access or reuse. It's a critical component for businesses, government agencies, and individuals operating in industries where data security is paramount. The core principle revolves around creating a formal, signed document that confirms the destruction of data, providing a clear audit trail.

The template itself is designed to be adaptable to various data types and destruction methods. It typically includes sections for:
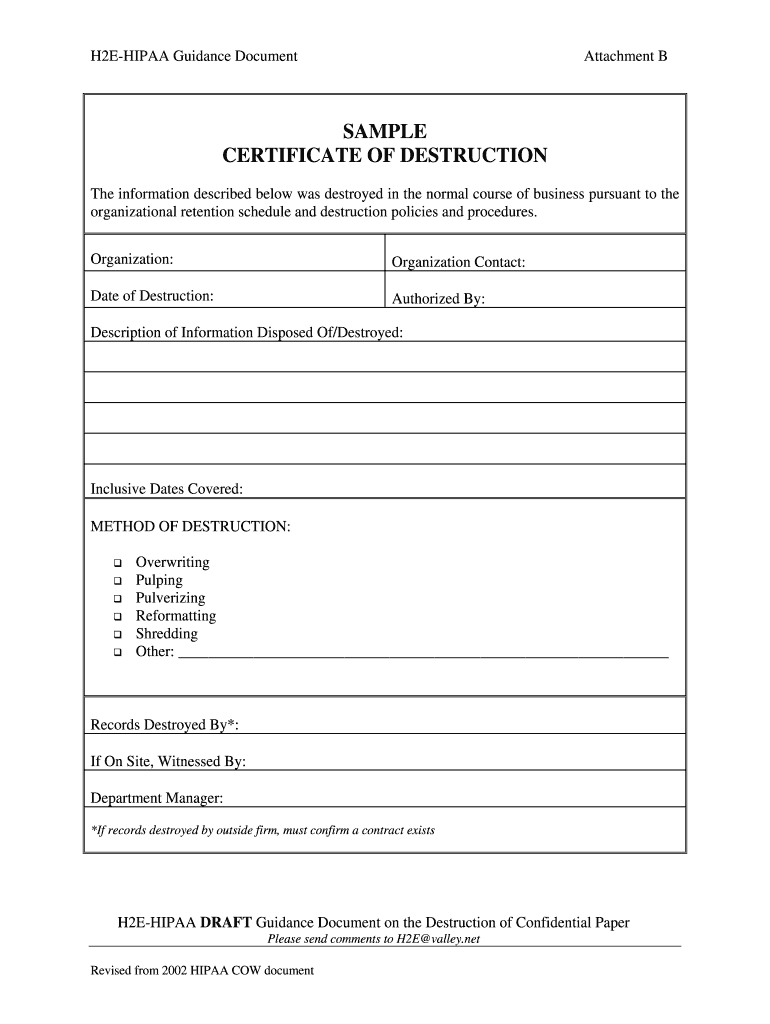
- Data Identification: A clear description of the data to be destroyed.
- Destruction Method: Specifies the method used for destruction (e.g., incineration, data wiping, physical destruction).
- Timestamp: Records the date and time of the destruction.
- Signature: A digital signature or handwritten signature from the individual responsible for the destruction.
- Documentation: A detailed record of the destruction process, including photographs or other evidence.
The effectiveness of a "Free Certificate of Destruction Template" hinges on its thoroughness and adherence to best practices. A poorly constructed template, lacking proper documentation or a secure signature, can be rendered useless. It's vital to understand that this is not a substitute for proper data security policies and procedures. It's a supplementary tool, designed to enhance existing safeguards.

Understanding the Template's Components
Let's break down the key sections of the template and their respective functions. The first section, "Data Identification," is absolutely critical. It requires a precise and unambiguous description of the data to be destroyed. This includes identifying the type of data (e.g., customer records, financial statements, medical records), the volume of data, and any sensitive information contained within. Vague descriptions can lead to misinterpretations and potential legal challenges. For example, simply stating "customer records" is insufficient; it needs to specify which records and their associated details.

The next section, "Destruction Method," outlines the chosen method for permanently removing the data. Incineration is often preferred for paper-based data, while data wiping utilizes specialized software to overwrite the data multiple times. Physical destruction, such as shredding or cutting, is suitable for hard drives and other storage media. The template should clearly specify the chosen method and justify its suitability for the data being destroyed. It's important to note that the chosen method must be compliant with relevant regulations and industry standards.

The "Timestamp" field is crucial for establishing a clear audit trail. The template should allow for the recording of the date and time of the destruction, ensuring that the destruction was performed within a defined timeframe. This timestamp is essential for tracking the lifecycle of the data and for potential legal investigations. Consider using a secure timestamping mechanism to prevent tampering.

The "Signature" section is where the responsibility for the destruction is formally acknowledged. A digital signature, generated using a secure platform, provides a verifiable proof of the individual's authorization to perform the destruction. This significantly reduces the risk of fraudulent destruction. The signature should be unique to the individual and should be digitally signed using a strong cryptographic key.

Finally, the "Documentation" section is where the detailed record of the destruction process is captured. This should include photographs or videos of the destruction process, as well as a written description of the steps taken. This documentation is vital for demonstrating compliance with legal requirements and for providing a clear audit trail. It should also include information about the disposal method used and any relevant certifications or permits obtained.

Utilizing the Template for Specific Scenarios
The "Free Certificate Of Destruction Template" is particularly useful in several scenarios. For example, in the legal field, it can be used to securely destroy evidence in criminal investigations. Similarly, it can be employed in financial institutions to ensure the secure destruction of sensitive customer data. Government agencies often utilize this template for the destruction of classified information. Furthermore, businesses can leverage it to comply with data privacy regulations like GDPR and CCPA, ensuring that customer data is securely deleted when it's no longer needed.
The template's flexibility allows for customization to meet specific needs. For instance, it can be adapted to include sections for specific data types, such as social security numbers or credit card numbers. It can also be integrated with existing data loss prevention (DLP) systems to automate the destruction process. The key is to tailor the template to the specific requirements of the application.
Considerations and Best Practices
While the "Free Certificate Of Destruction Template" offers a valuable tool for data destruction, it's essential to approach it with caution and adhere to best practices. It's not a substitute for robust data security policies and procedures. Furthermore, it's crucial to ensure that the template is properly implemented and maintained. Regularly review and update the template to reflect changes in regulations and industry standards.
One critical consideration is the security of the template itself. The template should be stored securely, with access restricted to authorized personnel only. Protecting the template from unauthorized access is paramount to preventing misuse. Consider using encryption to protect the template's contents.
Another important aspect is the training of personnel who will be using the template. They need to understand the proper procedures for using the template and the importance of adhering to best practices. Proper training can significantly reduce the risk of errors and ensure that the template is used effectively.
Finally, it's vital to comply with all applicable laws and regulations regarding data destruction. These regulations vary by jurisdiction and may include requirements for notification to data subjects and for secure disposal of data. Consult with legal counsel to ensure compliance with all relevant requirements.
Conclusion
The "Free Certificate Of Destruction Template" represents a valuable tool for organizations seeking to securely destroy data and comply with legal requirements. Its adaptability, combined with its clear documentation requirements, makes it a versatile solution for a wide range of applications. However, it's crucial to remember that this template is not a silver bullet. It's a component of a comprehensive data security strategy, and its effectiveness depends on proper implementation, ongoing maintenance, and adherence to best practices. By understanding the template's capabilities and limitations, organizations can leverage it to protect their valuable data and mitigate potential risks. The continued evolution of data security necessitates a proactive and adaptable approach, and the "Free Certificate Of Destruction Template" remains a key element in that strategy.
Conclusion
The "Free Certificate Of Destruction Template" offers a practical and relatively straightforward method for securely destroying data. While it's not a foolproof solution, its structured approach and documented process significantly enhance accountability and reduce the risk of data breaches. Proper implementation, ongoing maintenance, and adherence to legal requirements are paramount to ensuring its effectiveness. As data security threats continue to evolve, this template will undoubtedly remain a valuable tool for organizations seeking to protect their sensitive information. Ultimately, a layered approach to data security, incorporating technology, policies, and trained personnel, is the most effective strategy for safeguarding valuable data assets.
0 Response to "Free Certificate Of Destruction Template"
Posting Komentar